Now that management server is ready for action we can use it for first configuration task.
In my last post I’ve prepared a private SSH key in which I am going to use in order to secure a connection between Ansible management server and managed nodes.
Since this action will be required on all managed servers I am going to create an ansible role called “base” and include all hosts. This way tasks like deployment of private key or installation of prerequisite software can be done on all nodes in the environment.
Within the project structure I have created directory called “roles” in which I am going to separate tasks and files affiliated with given role.
In every role type directory I have created folder called “tasks” which contains file main.yml which is going to be called from a playbook responsible for given role. Below you can find screenshot of main.yml file of base role:
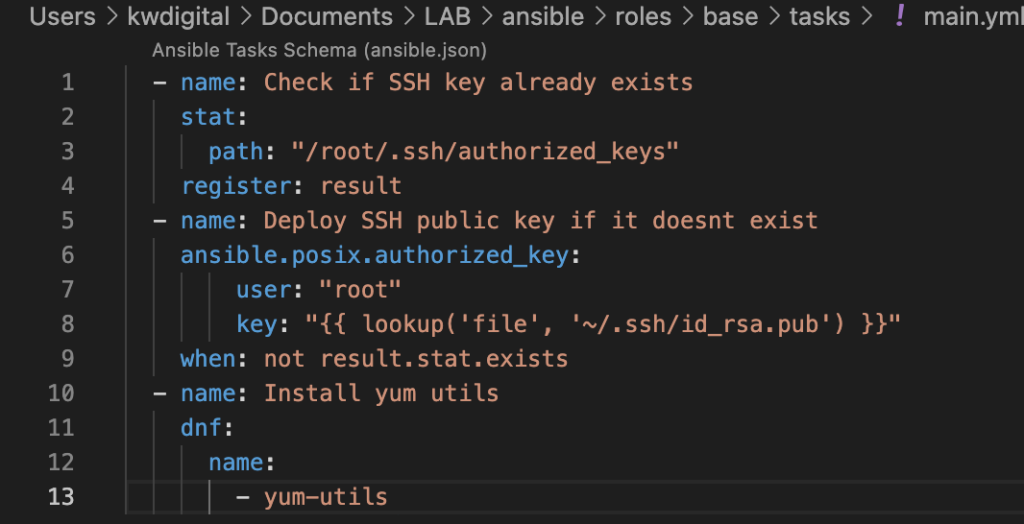
This is fairly simple example, but thanks to roles setup it allows for flexibility and scaling. In this case I am checking whether /root/.ssh/authorized_keys file exists on managed node. If not, I am deploying public key of management server to other nodes. Another action being done is installation of yum-utils package.
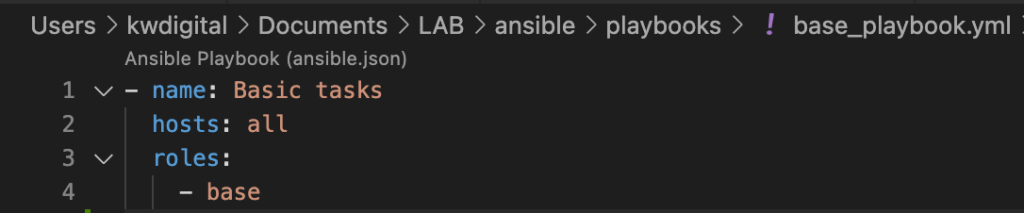
In order to run the commands a playbook is required. All it requires is to point to given role and hosts on which it should be executed. Base playbook looks like this:
In order to execute it, navigate to folder containing the .yml playbook and run following command:
ansible-playbook ./base_playbook.yml Since we have noted on which hosts (all) playbook should be executed, it is not required to point to a specific inventory file or group name.
After running the command you should receive output similar to screenshot below:
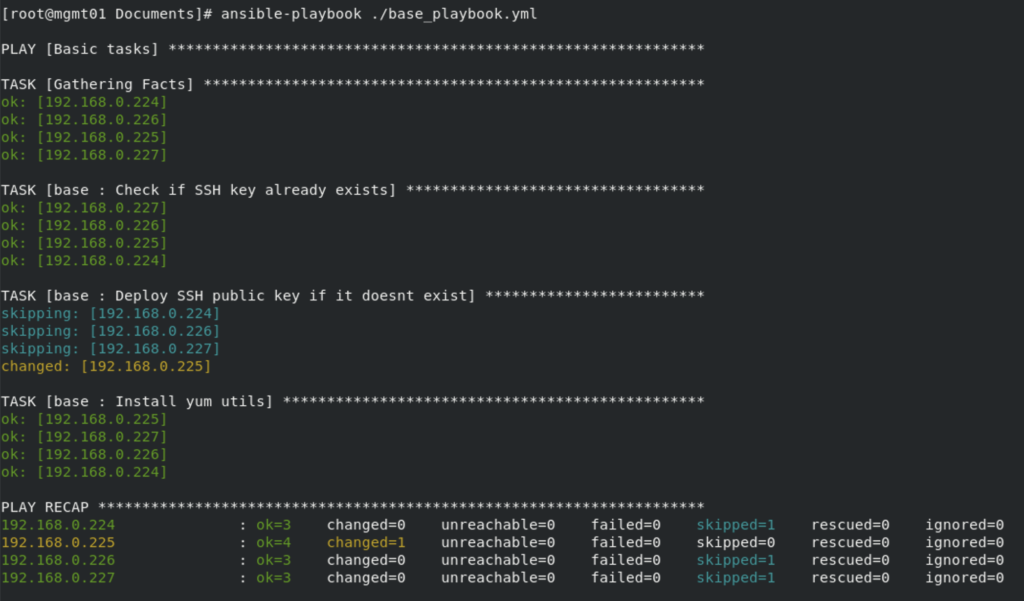
That’s it, all our hosts have received a basic configuration in form of SSH key deployment and installation of additional software.
In my next post I will dive deeper into configuration of management server, including installation of Jenkins.